Infrastructure: counter-attack anno 2019
On the 10th of October I went to the Young Potential Classes organised by Orbid. When I arrived in O’Learys Gent, I got the option between a few lectures. I chose the ‘Infrastructure: Counter-Attack anno 2019’ lecture because I’m really interested in Cybersecurity.

The lecture had a really interesting topic: how do computers and networks get infected even with all the new defence mechanisms in place.
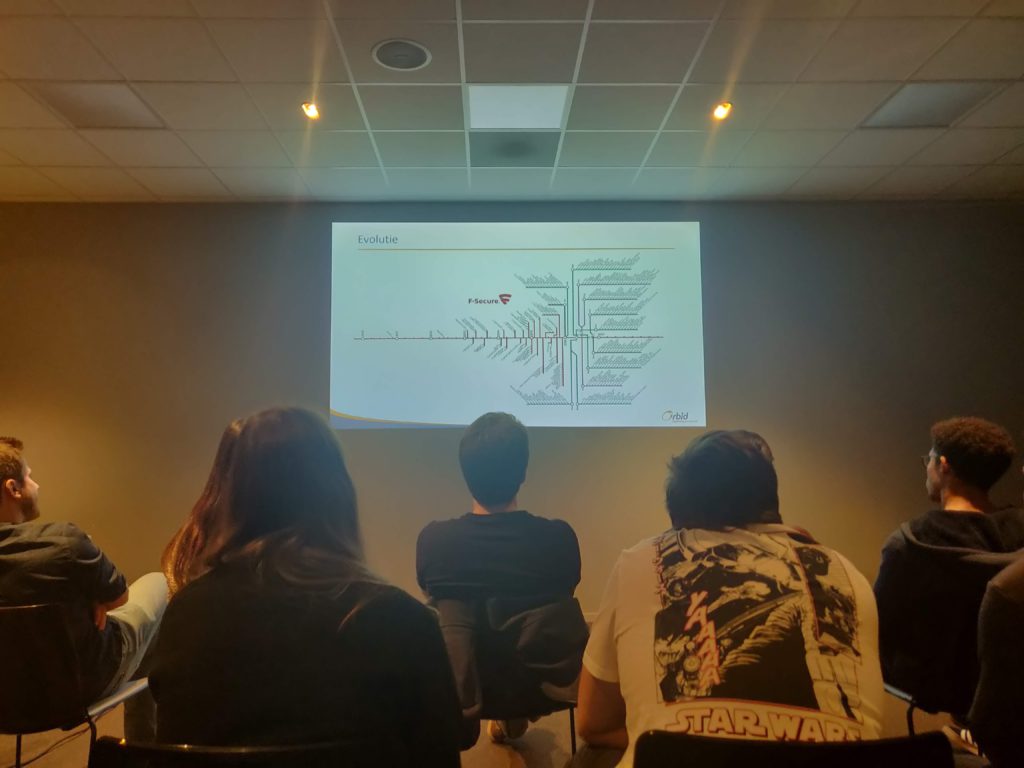
How could a ransomware attack like WannaCry infect more than 300 thousand computers in less than 5 days? After a brief summary of cyber security techniques, they started getting into the interesting stuff. Nowadays programs get put into a sandbox to determine the effects they have on a computer. In a sandbox the program gets everything it wants, like if the program wants to connect to a website they get the HTTP/1.1 200 OK status code even if the website isn’t registered.
This is how WannaCry got disabled once the killswitch was discovered by researcher Marcus Hutchins. Marcus discovered the worm first checks the killswitch domain name. When the domain wasn’t found it would start encrypting the computers data. So Marcus reacted fast by registering the domain “killing” the worm.
After a really interesting lecture, we had the possibility to bowl. Together with some people from Howest and people from Orbid we played a game.

After a competitive game, there was a networking moment with the Orbid employees. There were different drinks and American themed snacks available. Because I wanted to take the last train to Bruges, I didn’t have a lot of time to connect with these people. I want to thank Orbid for inviting me to this interesting event.